Financial institutions are consistently in the top-five list of cyber attack targets, with the greatest increase in data breach risk coming from outside hackers.[1] Customer financial records and associated personally identifying information are high-value commodities on the dark web. Nonetheless, consumers expect banks and other financial institutions to provide secure online services and access. Creating sufficiently secure online banking is a primary reason financial institutions use ThreatModeler™.
Secure Online Banking with ThreatModeler™
Click to watch a brief video on how easy it is to generate actionable threat models with ThreatModeler™.
Why Secure with Threat Modeling
For April’s Threat Model of the Month series, we chose to generate a pair of threat models that may be used by banks and other financial institutions. The first threat model is for an application which is intended to allow authenticated customers to check their statements, update their profile information, or to transfer funds between financial institutions. The application also includes a credit check for new users.
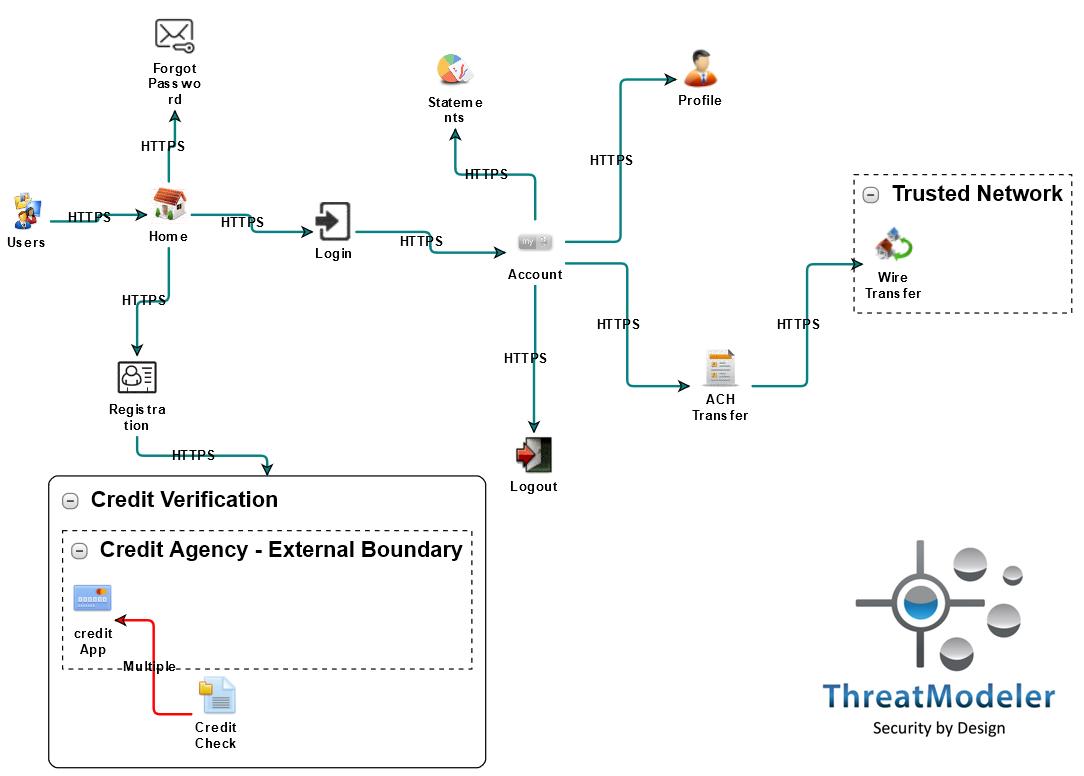
The threat model diagram shown above maps how users may navigate from the application’s home page through various use cases (represented by icons on the diagram). Of particular importance regarding secure online banking, we should note that several of the identified use cases require data attackers consider high-value. In particular:
- The Forgot Password use case requires the user’s username and email address;
- The Registration use case requests username, password, and certain personally identifying information;
- The Login use case, of course, asks for the user’s username and password;
- The Profile use case, in addition to other information, allows users to update their name and address;
- The ACH Transfer use case may allow users to transfer funds to vendors or other individuals; thus it asks for account and routing numbers, as well as the name and address of the recipient;
- The Credit Verification process will require the users’ social security number, date of birth, and personal identifying information.
In other words, this application processes all the data types financial institution hackers seek. Providing secure online banking will make securing applications such as this, a priority for the organization.
Increase Security for Online Banking by also Threat Modeling the Operational System
Addressing today’s evolving cybersecurity challenges cannot be done by guesswork. Nor, thanks to the degree to which we operate within a highly interconnected cyber ecosystem, can security be achieved by considering individual applications in isolation.Creating and maintaining secure online banking requires threat modeling both the applications and the operational systems on which they are accessed. The operational threat model to the right allows users to identify threats inherent to the operational environment.
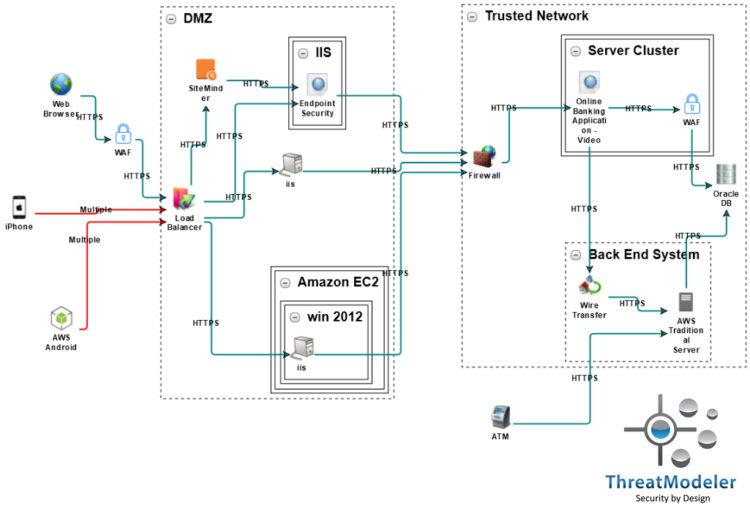
The operational threat model above allows users to identify threats inherent to the operational environment. Moreover, ThreatModeler’s unique ability to nest threat models – note the Online Banking Application threat model in the Server Cluster – allows organizations to study threats inherent to application interactions, understand the upstream sources, and quantify the downstream impact of any realized threat.
Genuine, risk-reducing security can only be achieved by understanding the “big picture,” from the attacker population to tracking the organization’s comprehensive attack surface across all applications within the operational environment. An enterprise threat modeling process that scales across the entire DevOps portfolio, built upon the ThreatModeler™ platform, will consistently produce the outputs CISOs need to quantify and reduce their organization’s overall risk – while at the same time yielding the role-based outputs other organizational stakeholders need.
Both threat models diagrammed above were built in about 25 minutes by a non-security expert. The summary threat model report for the online banking application can be downloaded here, and the summary report for the operational threat model – which includes the 91 threats from the nested Online Banking Application threat model – can be downloaded here.
Request a Demo to learn more about how the ThreatModeler™ platform helps organization secure online banking.
[1] Huq, Numaan. “Following the Data: Analyzing Breaches by Industry.” Trend Micro, Inc: Tokyo. 2015.






