Stalkerware is one of the most invasive forms of cybercrime and involves the use of spyware that is freely available on the market. Once installed on a device, stalkerware, in stealth mode, remains undetected. Here is where stalkerware earned its name and remains one of the most dangerous types of malware. Malicious actors will use stalkerware for surveillance activities and harassment – either intentionally or unintentionally. In severe cases, cybercriminals will initiate stalking and, in the worst cases, enact violence against the victim.
Stalkerware straddles a fine line and, traditionally, hasn’t been clearly defined like some of the more traditional forms of malware cybercrime, such as phishing. Up to this point, stalkerware is difficult to detect. Confusion over the legality of stalkerware has also made it difficult to bring to the court of law, partially because there is no steadfast, legitimate way to obtain forensic evidence that it is happening. Despite its obscurity in relation to other malware, stalkerware remains pervasive as a serious threat. Anyone with access to commercially available spyware can partake in stalkerware.
Grave Seriousness of Stalkerware and the Statistics Are Scary
It’s a serious issue and the statistics are scary, according to a recent NortonLifeLock survey. The antivirus company issued the following statement:
“Online creeping, or following someone persistently or stealthily online, is typically benign behavior. However, when that becomes a pattern of behavior or escalates to using the same technology and tactics to harass someone online, it’s cyber stalking. Cyber stalking can take on many forms, but the common denominator is that it is unwanted, obsessive and sometimes illegal.”
The statistics from the survey are staggering: 29% of respondents said they spied on their current or former partners. The numbers between males and females differ – 15% of men, and 6% of women admitted to using an app to spy on a current or former partner’s device use. Monitoring activity include text messages, phone calls, direct messages, emails and photos. The stalkerware problem can be higher, since many people would not admit to participating in abusive behavior. Cyberstalkers are also under-prosecuted compared to other harassment, violence and abuse due to the sensitive, private nature of these cases.
Legal and Technical Confusion About Stalkerware
Historically, antivirus companies did not effectively define stalkerware as malware, even though it behaves like malware once it is installed on the device. Since this has not been clearly defined, stalkerware leaves antivirus companies in a legal grey area. At some point, they may be held accountable and sued for not protecting consumers.
A not too dissimilar case occurred when Enigma Software sued Malwarebytes, a creator of antivirus solutions. Malwarebytes detected, flagged and put a block on two of Enigma Software’s applications that it deemed potentially unwanted programs (PUPs): SpyHunter, an adaptive malware scanner and removal tool, and RegHunter, a Windows Registry and data file cleanup tool. While neither are forms of stalkerware, they were designated as PUPs and blocked from user devices.
The case was eventually dismissed. However, the issue arises as to whether or not Malwarebytes is looking out for the safety and security of its consumers by blocking SpyHunter. Stalkerware apps are intended for legal use, such as monitoring your kids who are minors or keeping track of employee activity on mobile devices issued by the company. In fact, spyware manufactures often market their tools as children-monitoring solutions.
Anatomy of a Stalkerware Threat Model
Stalkerware has been so elusive in clearly defining, that even technology developers and security experts have used the incorrect threat model to think like a hacker, determine who would leverage stalkerware and learn the tell-tale characteristics that a victim is being abused. A domestic-abuse threat model is the missing component but the details are not so obvious – to so many people, apparently. The stalkerware threat model includes the following components:
- Physical proximity to the target
- Threats of violence
- Access to the target’s device
- Intention to elicit control over the victim
- Other acts of manipulation including fear tactics, e.g. informing the victim you know the content on their device
Cyberstalkers Leverage Stalkerware Stealth Mode to Hide From Victims
Oftentimes, stalkerware uses spyware stealth features that make it difficult to detect the so called “parental-monitoring” app installed on the device. There are other options out there that don’t feature a stealth mode, plus make it clear that the monitoring app is installed – usually with an app icon. Yet spyware makers take advantage of the legitimacy attributed to parental- and employer-control apps. According to NortonLifeLock, a company quickly changed their app name from “Girlfriend Cell Tracker” to “Family Locator for Android.'”
Since stalkerware is achieved through legally manufactured tools, typical antivirus software does not easily detect or remove it. Using traditional processes to remove malware may further endanger the victim by alerting the cybercriminal that s/he knows they’re being preyed upon. That danger may manifest via abuse that can be digital and physical. In the meantime, due to the sensitive nature of stalkerware, remediation varies from instance-to-instance.
Stalkerware Takes Priority with Law Enforcement and in the Courts as Awareness Grows
According to Laura-Kate Bernstein, senior counsel in the Department of Justice’s Computer Crime and Intellectual Property Section, Cyberstalker cases presented to the federal court level has increased year-over-year since 2014. Law enforcement agencies are now beginning to handle stalkerware domestic violence cases with urgency, after formerly devoting less resources to the issue. But a number of leading companies that have the potential to mitigate stalkerware have not yet enrolled in a solution.
For example, tech giants such as Apple, Google and Microsoft don’t have an official way to combat stalkerware. Google expressly forbids stalkerware in policies related to the Play Store. It’s about time more spyware manufacturers and cybersecurity firms properly address the issue of cyberstalking and stalkerware. In an ideal world, antivirus apps can, for instance, identify, flag and deliver forensic evidence to law enforcement and the courts that demonstrate that cyberstalking occurred.
The FTC banned Retina-X sales for multiple hacks on its servers where the cybercriminals stole data. Retina-X can be considered stalkerware and has more than 15,000 downloads. Future bans on stalkerware based on a company’s ability to meet security and compliance requirements from external regulating bodies may follow suit. Google promptly pulled seven Android stalkerware applications after being notified by Avast, an antivirus developer. But not until the stalkerware was downloaded 130,000 times.
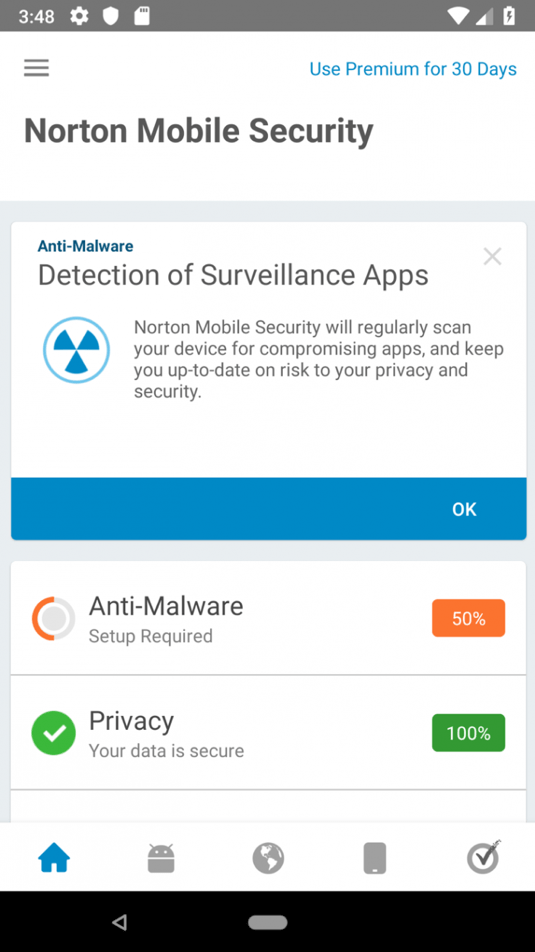
NortonLifeLock has developed CreepRank as a new feature on its Norton Mobile Security application. CreepRank helps to more accurately measure the degree of stalkerware on apps with anonymized data about billions of app installations on 50 million mobile devices. Years of data is covered. CreepRank measures the propensity for a surveillance app to be considered “creepware” – those apps that can be used with malicious, abusive intent and, in worst cases, lead to intimate partner violence. CreepRank found 1,000 of the highest listed CreepRanks can be used in an abusive manner.
Coalition Against Stalkerware Formed by US and European Organizations to Address the Problem
Stalkerware is a dangerous issue and a group of security companies, including NortonLifeLock, the National Network to End Domestic Violence and Kaspersky, among other notable companies, started a coalition against it. In addition to putting a stop to the harassment, abuse and violence that is involved with stalkerware, the Coalition Against Stalkerware seeks to raise awareness on the topic. Formed in mid-2019, the Coalition Against Stalkerware includes antivirus developers, domestic-abuse awareness organization and the Electronic Frontier Foundation. The Coalition Against Stalkerware structure involves organizations in the US and Europe. Its goals include:
- Defines the best practices to approach conversations on stalkerware
- Educate and train consumers about stalkerware
- Identify technologies that are deployed on devices without the user’s permission
- Embolden learning about stalkerware – within organizations and by security professionals
- Improve cybersecurity tech response to stalkerware by presenting known use cases to IT security vendors
- Create ways to test anti-stalkerware solutions
- Set criteria to detect stalkerware
- Advocate for victims and survivors through technology development and with related service organizations
Webinar – How to Achieve Secure CDLC through Threat Modeling Hosted by Cybersecurity Tech Accord
On Wednesday, February 26th 2020, ThreatModeler will present a webinar on achieving secure cloud development life cycle through threat modeling. The webinar will dive into the best practices involved in visualizing your cloud attack surface in order to identify, prioritize and mitigate cyber threats. Alex Bauert, Senior Director of ThreatModeler’s Threat Research Center, will be on hand to talk about the migration to the cloud and how to “shift left” security.
About Alex Bauert
Alex Bauert has more than 25 years of IT experience, with 15 of those years spent in architecture and application security leadership roles. Bauert is currently the Senior Director of ThreatModeler’s Threat Research Center, where he drives the maintenance and updating of the Threat Intelligence Framework. Bauert speaks four languages fluently and coaches high school and club soccer.





