Threat modeling has a well-proven capacity to provide agile DevOps teams a “security heads-up,” during project design, especially in cases where application security is a critical priority. In our previous article comparing Microsoft’s Threat Modeling Tool (TMT) to ThreatModeler™, we considered several key factors to securing applications at the speed and scale of modern DevOps teams. In this article, we want to extend that discussion and consider outputs beyond AppSec.
When it comes to ThreatModeler vs. TMT from an AppSec perspective, we noted three significant differences:
- The time it took a security expert to create equivalent threat models of a smart home in both TMT and ThreatModeler (approximately one hour for the TMT threat model and 15 minutes with ThreatModeler);
- The number of potential threats identified by each tool for the smart home threat models (36 identified by TMT; 142 identified by ThreatModeler); and
- The ease with which non-security teams could utilize the threat model (TMT requires security subject matter experts at all stages of output utilization; ThreatModeler’s outputs can be automatically integrated into existing DevOps and QA team workflows).
However, very few persons in the organization will appreciate these outputs beyond the groups directly responsible for the functionality, security, and time-to-delivery of a particular project. The CISO, senior executives, and the board of directors will consider the security of an individual application as an “in-the-weeds” issue – something we pay smart people to handle. Senior executives and the board have neither the expertise nor the bandwidth to celebrate one completed project, regardless of how functional and secure it is. Their plate is full with organizational-wide strategic and fiduciary matters – big-picture stuff. The CISO, of course, is in the challenging role of translating the “in-the-weeds” details of the organization’s real-time threat portfolio and risk profile into a strategic and fiduciary “big-picture.” To do so, the CISO needs threat modeling outputs beyond AppSec.
Outputs Beyond AppSec for the CISO
Let’s see, then, what can be offered to the CISO by ThreatModeler vs. TMT in the following categories:
- Understanding the organization’s comprehensive attack surface;
- Objective “what-if” analysis of the effectiveness of deployed or contemplated compensating controls; and
- The ability to help the CISO prioritize where to invest limited security resources.
CISOs need to Analyze the Comprehensive Attack Surface
Microsoft Threat Modeling Tool, as a stand-alone product, does not provide analysis of any attack surface – it only identifies categories of threats within the STRIDE scheme. In 2012, however, Microsoft released another free tool – conveniently dubbed Attack Surface Analyzer (ASA).[1] The ASA was designed to help developers understand how changes in applications modify the attack surface of a Windows operating system. The tool has been appreciated by developers working that particular niche. Like TMT, however, ASA is a static tool. It allows users to compare “snapshots” of information related to the security of a Windows environment before and after system changes are made – rather like looking at a brochure promoting a weight-loss system. There is, admittedly, some limited usefulness for such a static comparison, but the outputs of the ASA are, again, geared for those individuals who work “in the weeds.” Neither TMT nor ASA, together or in tandem, provide the useful high-level perspective of the organization’s comprehensive attack surface needed by CISOs.
On the other hand, ThreatModeler™ automatically and dynamically produces outputs beyond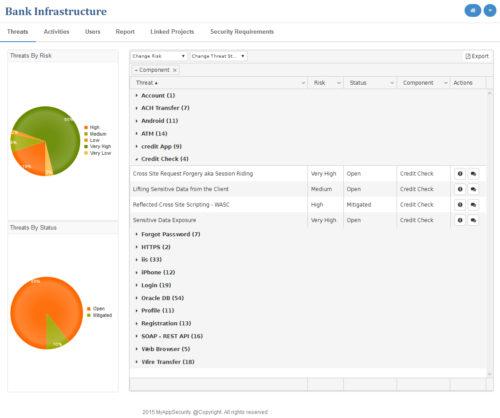 AppSec which the CISO can take to senior executives. As individual threat models are built and modified by various teams throughout the organization, ThreatModeler’s integrated Attack Surface Analyzer combines and collates the various outputs for analysis. The ThreatModeler Attack Surface Analyzer™ allows CISOs to
AppSec which the CISO can take to senior executives. As individual threat models are built and modified by various teams throughout the organization, ThreatModeler’s integrated Attack Surface Analyzer combines and collates the various outputs for analysis. The ThreatModeler Attack Surface Analyzer™ allows CISOs to
- Apprehend which specific threats impose the greatest risk across the entire DevOps portfolio and drill down to the source of each threat;
- Identify the individual DevOps projects which contribute the greatest risk to the organization and examine threats by architectural component, risk, and status;
- Study in real-time the changes in carried risk as various stakeholders throughout the organization create new and modify existing threat models;
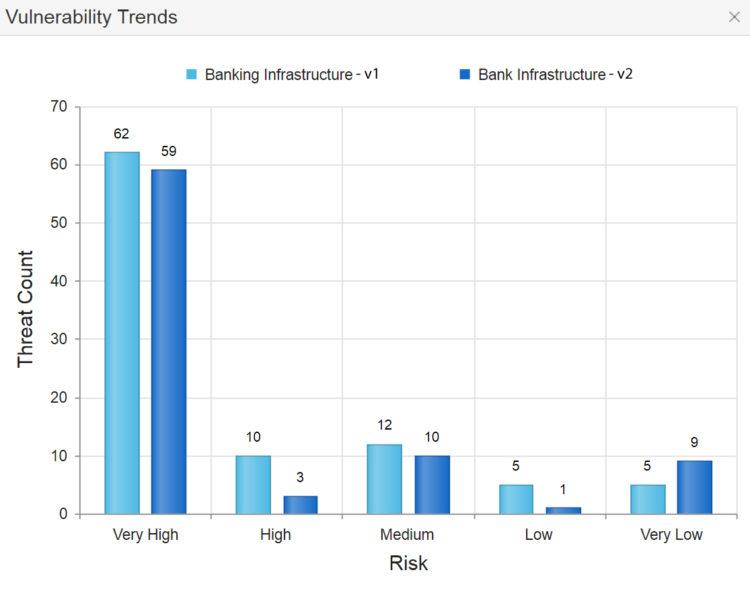
- Track organization-wide threat and vulnerability trends over time;
- Understand which new threats are relevant to the organization and real-time, and analyze any potential downstream impact; and
- Define custom, detailed threat model reports.
CISOs need to Evaluate the Effectiveness of Compensating Controls
Neither of Microsoft’s free tools offers CISOs anything by way of helping them assess the effectiveness of compensating controls. TMT and ASA do not provide outputs beyond AppSec for applications considered in isolation.
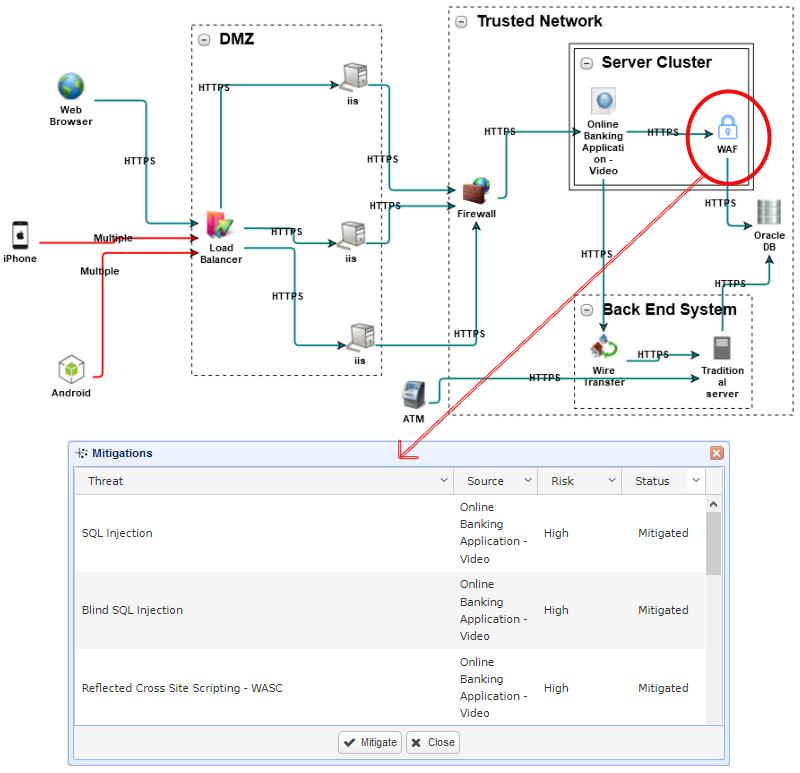
ThreatModeler™, on the other hand, provides many outputs beyond AppSec, making it easy for security professionals and CISOs to conduct dynamic “what-if” analysis of the organizational effectiveness of deployed and planned compensating controls. Analysis can be carried out for endpoint security, cloud-based or on-premises deployment environments, IoT and mobile devices, industrial control and cyber-physical systems, applications, and any combination thereof.
Two unique features that only ThreatModeler™ offers facilitates the analysis of compensating outputs beyond AppSec:
- ThreatModeler’s unique architecturally based process flow diagrams allow users to treat completed threat models as architectural components of other threat models. In other words, threat models can be nested within threat models – and nesting can be done to any depth. Threats from nested threat models can be imported into the active threat model so that users can study the effects of application interactions, shared components, and 3rd party systems, and analyze the downstream impact of relevant threats.
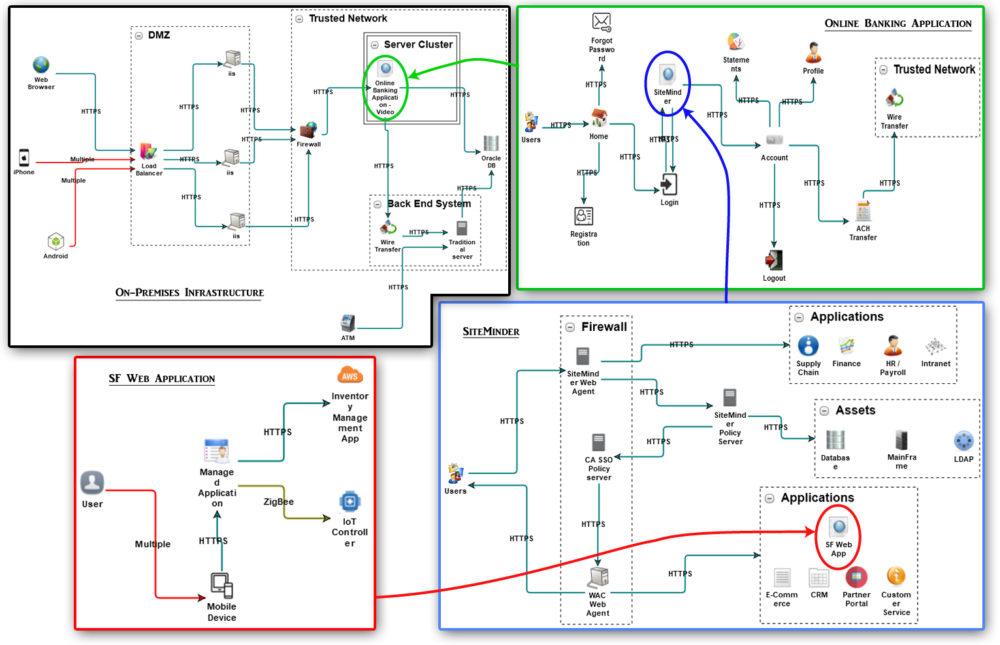
- ThreatModeler also treats compensating controls – whether deployed or contemplated – as architectural components which can be added to any threat model. Compensating control components model the mitigation of specific threats, and may be applied in any number or combination to a threat model, allowing users to determine the best configuration of controls for a given system.
CISOs need to Prioritize Investment of Limited Resources
Microsoft’s TMT and ASA provide limited outputs for “in-the-weeds” security subject matter experts. Such outputs can be helpful when considering security issues of single applications in isolation.
ThreatModeler™ provides outputs beyond AppSec for a multitude of organizational stakeholders, including the CISO. The integrated attack surface analyzer and executive dashboard summarize the entire threat model portfolio, yielding critical, high-level data for the CISO to analyze as part of determining organizational security priorities and where to invest limited resources to generate the greatest ROI.
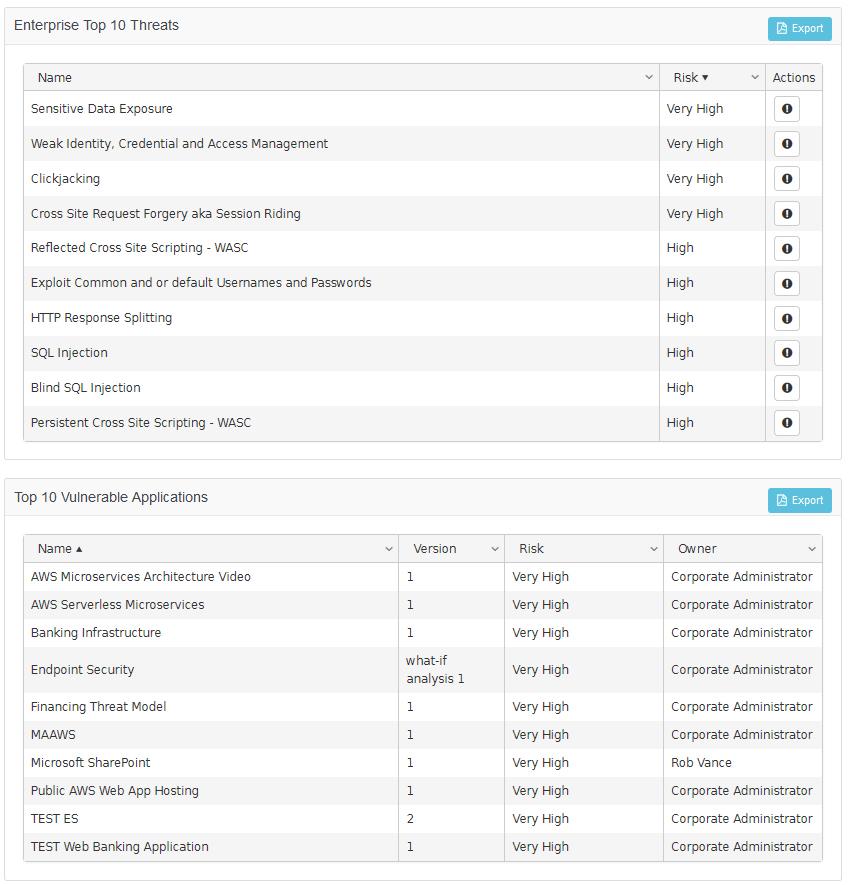
ThreatModeler™ outputs beyond AppSec include a rolling list of the top-ten threats organization-wide and a rolling list of the top-ten most vulnerable DevOps projects. Various versions of threat models may be analyzed together for vulnerability trends – to see how changes in project business requirements affect the organization’s risk profile.
Schedule a demo to learn how ThreatModeler can provide outputs beyond AppSec for stakeholders across your organization.
[1] Rains, Tim. “Microsoft’s Free Security Tools – Attack Surface Analyzer.” Microsoft Secure Blog. Microsoft: Redmond. August 2, 2012.





