ThreatModeler has seen a significant uptick in US federal government agencies and contractors approaching us to find out more about automating the labor intensive manual process of threat modeling. Those charged with proactively managing NIST 800-53 Rev. 5 requirements at scale quickly realise ThreatModeler stands out as solving their multiple challenges of secure design, automation, tracking & enforcing regulatory standards, visual architectural diagram output and so much more.
Earlier in May the Biden Administration executed an Executive Order on Improving the Nation’s Cybersecurity, and HelpNetSecurity made a poignant observation: “One can’t help but notice the several allusions to automation in this document. Automation has been mentioned right from the supply-chain and code stage to the vulnerability management stage to the detection of threats. The EO has done everything except mention DevSecOps.”
While there is no explicit mention of DevSecOps – nor threat modeling – in the Biden EO, these are alluded to, but automated threat modeling and DevSecOps are explicitly presented in the newly released Department of Defense document entitled: DevSecOps Fundamentals Guidebook: DevSecOps Tools & Activities.
The document introduction begins with this statement on Page 6:
“The goal of DevSecOps is to improve customer outcomes and mission value through the automation, monitoring, and application of security at every phase of the software lifecycle.
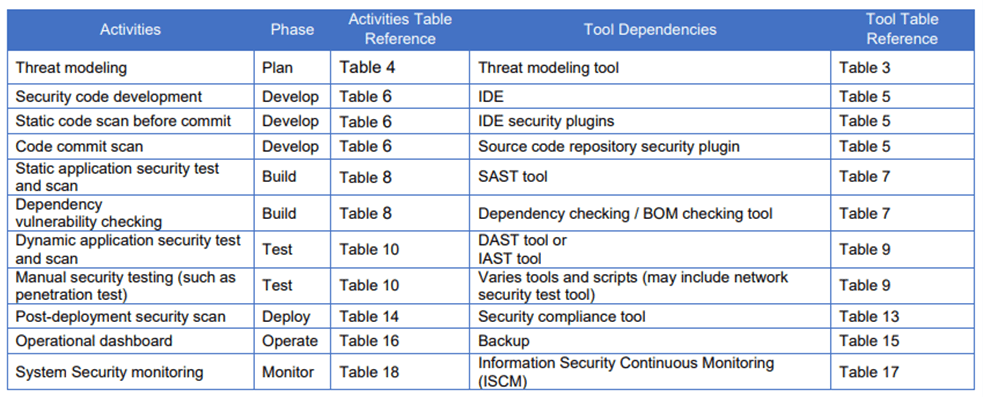
Practicing DevSecOps requires an array of purpose-built tools and a wide range of activities that rely on those tools. This document conveys the relationship between each DevSecOps phase, a taxonomy of supporting tools for a given phase, and the set of activities that occur at each phase cross-referenced to the tool(s) that support the specific activity.”
This is an extremely heartening and forward-thinking document and it gets better yet as the very first purpose-built tool listed is for threat modeling!
Table excerpt from Page 8 below:
As proponents of DevSecOps and of course threat modeling automation, ThreatModeler wishes to convey to our Federal colleagues we stand ready to partner with you to begin your DevSecOps journey.
From our discussions with federal agencies we know cloud migration, automation, secure design and regulatory standards are all top priorities and the brief 2 minute overview video below entitled: Build a Threat Model With Just One Click, will give you a taste of just one of the advanced capabilities ThreatModeler affords you for the Cloud.
ThreatModeler comes with regulatory compliance frameworks out-of-the-box including those pertinent to Federal Agencies including: NIST 800-53 Rev. 5, NIST 800-171, and CMMC. You can now track and enforce adherence throughout the SDLC with ease.
Contact us for a demo to see for yourself how ThreatModeler’s automation saves days and weeks of GS-13’s time building manual threat models.
-The ThreatModeler Fed Team





