Organizations are becoming increasingly digital-driven, causing the business world to become highly interconnected. Relationships between organizations and their vendors, suppliers, and distributors are now remotely managed across global networks. Evolving customer experience is increasingly impacted by an organization’s online presence. Board and C-level executives take notice when competitors report 20-30% or greater EBITDA improvement through digitally-generated insights and improved efficiencies.[1] Becoming a market leader in this highly interconnected world requires data-driven transformational leadership.
There is nothing special these days about simply being a digital organization. Having only internal and external-facing applications, is a long way from driving competitive advantage, value, and stockholder returns through the IT ecosystem.
The Stone Age of cyber is IT as a cost center. A good-enough position for cyber is that of a strategic enabler. The vanguard position of an organizational cyber ecosystem, however, defines the value-horizons across the enterprise. Reaching for this plateau is what digital transformation – and, more specifically, the DevOps transformational leadership – is all about.
Good coaches, just like good executive leadership, know how to produce peak performance. Transforming a runner into a contender for Olympic gold, however, requires more than just an ability to give personal or team motivation. Achieving the vanguard position cannot occur without leadership understanding the real-time data as it impacts the desired outcome.
Transformational Leadership Requires Data
CIOs, CSOs, CISOs or other business leaders seeking to maximize the organization’s benefits from digital transformation benefits are like Olympic coaches. Their transformational leadership may start with applying management concepts to initiate a culture change. However, a transformation that results in vanguard positioning only comes from monitoring the organization’s real-time data and applying a deep understanding of where that data places the organization in relation to its long-term goals.
Digital transformation is inseparably intertwined with creating an effective DevOps culture. DevOps is not a result nor a driver of digital transformation. It is the fuel.[2] An effective DevOps implementation is the difference between being a mediocre player or a market leader. Organizations with efficient DevOps implementation have a significantly higher production of customer-pleasing products. The net result is the ability to capture more significant market share and sustain higher profitability[3] – the gold standard of any transformative initiative. More than 27,000 respondents contributing across six years of research consistently demonstrate high-functioning IT departments strongly and positively correlated with higher operational performance across the whole organization.
However, the consistent stumbling block to effectively implementing DevOps– and, consequently, to efficiently transforming the organization – is security. It does little good to pump out more functional products if those products increase organizational risk from inherent insecurity. Effective transformational leadership that produces top-performing DevOps cultures are data-driven, which also requires something of a paradigm shift among leaders.
Data analysis must be holistic and provide an integrated approach to decision making. If not, it will get bogged down in complexity and sheer volume or run the risk of taking the leader on a snipe hunt. Creating a DevOps culture that fuels vanguard positioning is no accident: it comes from integrating security into the executives’ existing dataset.
Generating Transformational Leadership Security Data
Traditional DevOps includes at least one feedback loop. Environments utilizing CI/CD methods have multiple and continuous opportunities for feedback. However, much of this feedback is only related to production.
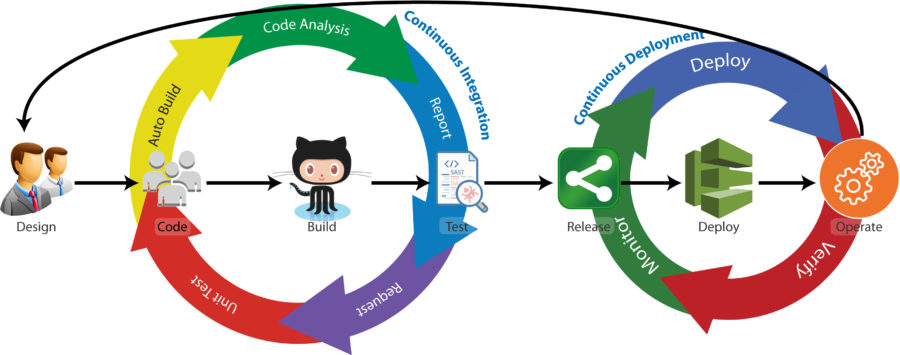
Making security an integral part of a DevOps CI/CD environment only happens through the impetus of transformational leadership. Previously in this series, we considered how security can be automatically implemented at the design whiteboarding stage, how to promote the cross-functional collaboration, creating up-front QA, and improving Ops visibility. In this installment, we consider generating a “big picture” perspective of the organization’s security for senior executives with attack surface analysis.
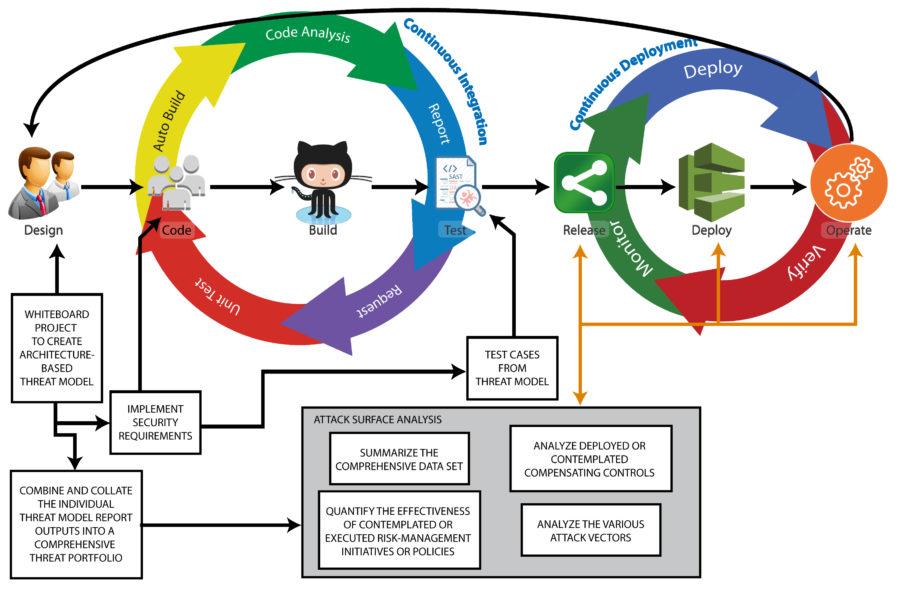
Architecturally-based enterprise threat modeling is far more than traditional, “proactive” application threat modeling. An enterprise threat model portfolio gives Ops personnel visibility into how the security of the infrastructure – whether on-premises or cloud-based – is impacted by the deployed or in-production applications. The outputs of the portfolio are further combined and collated to yield an enterprise-wide perspective on the organization’s cybersecurity position. Enterprise threat modeling creates the data needed by transformational leaders including:
- Quantifying the effectiveness of contemplated or executed risk-management initiatives;
- Providing analytical insight into the mitigations provided by planned or deployed compensating controls;
- Yielding real-time clarity into the probable attack paths and potential attackers; and
- Enabling deep understanding of the organization’s vulnerable points and highest priority threats.
Transformational Leadership Needs Two Types of Data
Transformational leadership needs to think ahead of the situation at hand. To that end, the data provided by enterprise threat modeling comes both from pro forma modeled outputs and from analysis of the active, deployed cyber environment.
The threat modeling platform generates pro forma data as soon as an application is whiteboarded. Pro forma data generation continues each time the application cycles through the CI/CD pipeline. What are the potential threats that will affect this application? Are there new threats relevant to this application? Furthermore, the threat model created or modified by the application architect are immediately available as architectural components for the deployment infrastructure threat model. Before development sprints begin, administrators will understand how the new or modified application will impact the infrastructure’s security.
Enterprise threat modeling, however, is not just for applications. Traditional, DFD-based threat modeling required significant documentation and hours of communication with cross-functional teams. Architecturally based threat modeling is so much more efficient. Creating a threat model of a deployed application or system is doable in a matter of minutes. As the threat model portfolio incorporates deployed applications and systems, executives have increased visibility into the organization’s cyber environment, allowing for data-driven quantification of the organization’s level of security in real-time for true transformational leadership.
Threat modeling is no longer just for high-risk applications. Nor it confined any longer to the domain of “in the weeds” security professionals. With an architecturally-based, enterprise threat modeling, CIOs, CSOs, CISOs and other executives have the data they need to provide the transformational leadership their organizations need. Threat modeling is now for executives, too….
Give your IT or security executive the data and outputs necessary for transformational leadership – Request a live ThreatModeler demo today.
[1] Gleeson, Brent. “The Benefits of Leading Data-Driven Organizational Change.” Forbes. Forbes Media: Jersey City. September 17, 2017.
[2] Rudder, Carla. “Five DevOps Leadership Priorities in 2018.” The Enterpriser’s Project. Red Hat: Raleigh. November 17, 2017.
[3] Forsgren, Nicole. “2017 State of DevOps Report.” DevOps Research and Assessment (DORA). Puppet: Portland. 2017.





