Where Snyk adds value:
✅ Continuous code and dependency analysis
✅ Pipeline-integrated security detection
✅ Developer-first workflows
ThreatModeler Platform &
Snyk knows what bad code looks like. ThreatModeler knows what secure architecture looks like.
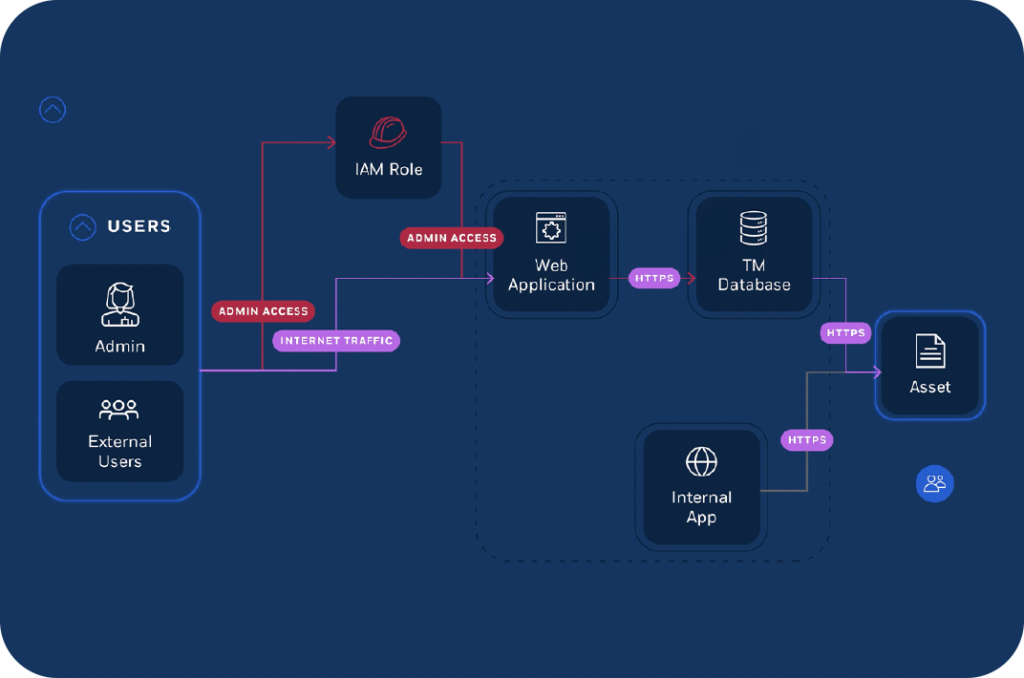
Model architecture, trust boundaries, and control strategy upfront
Give context to Snyk findings so teams fix what actually matters
Replace inconsistent analysis with repeatable, governed outcomes
Track threats, controls, and rationale across the SDLC

| Capability | ThreatModeler | Snyk Evo |
|---|---|---|
| Primary approach | Architecture-driven threat modeling | Code, pipeline & runtime analysis |
| Security focus | Continuous risk identification begins with secure design | Continuous detection & monitoring without secure design |
| Threat modeling methodology | Structured, open (STRIDE, PASTA, LINDDUN, etc.) | Not methodology-aligned |
| Audit-ready outputs | Yes – structured, repeatable, explainable | No – not designed as audit evidence |
| Compliance mapping | 180+ frameworks | Not aligned to compliance frameworks |
| Consistency of output | Deterministic, repeatable | AI-generated, variable |
| System of record | Persistent, governed threat models | Continuous analysis, not authoritative |
| Scope | Full system architecture (apps, cloud, AI, APIs) | Code + pipeline + runtime context |
✅ Continuous code and dependency analysis
✅ Pipeline-integrated security detection
✅ Developer-first workflows
❌ No formal threat modeling methodology
❌ No audit-ready outputs
❌ No Architecture-driven risk analysis
❌ No consistent, repeatable modeling
❌ No Secure design context

• Code and dependency analysis without architectural context
• Non-deterministic pipeline-integrated security detection
• Developer-first workflows without governance

✅ Consistent, enterprise-wide risk visibility and management
✅ Secure architectures that prevent surprise findings during pen testing
✅ Architecture-driven risk analysis across apps, cloud, and agents
✅ A system of record for security decisions at enterprise scale
✅ Accelerated time to market for products
10x
more threat models created in a large enterprise deployment
50%
reduction in effort
5x
faster model creation
2900+
components
100+
protocols
