10x
more threat models created in a large enterprise deployment
ThreatModeler Platform &
Better together: AI speed plus architecture-aware secure design.
Frontier models accelerate vulnerability discovery and remediation. ThreatModeler ensures those efforts are grounded in system intent, trust boundaries, and architectural context—so teams know what actually matters.
AI can generate fixes faster. ThreatModeler helps teams prioritize and implement those fixes in ways that align to intended design, control strategy, and real risk in context.
ThreatModeler captures architecture, threats, and control decisions upfront, then carries that governed context into AI-driven workflows so remediation is more consistent, relevant, and aligned across teams.
ThreatModeler operationalizes threat modeling across the SDLC with deterministic AI, governance, and a system of record—so organizations don’t just fix issues faster, they continuously reduce preventable risk.
Result: better AI output, stronger prioritization, less wasted remediation.
ThreatModeler operationalizes this with AI inside a deterministic framework—so security decisions are consistent, repeatable, and governed across the SDLC.
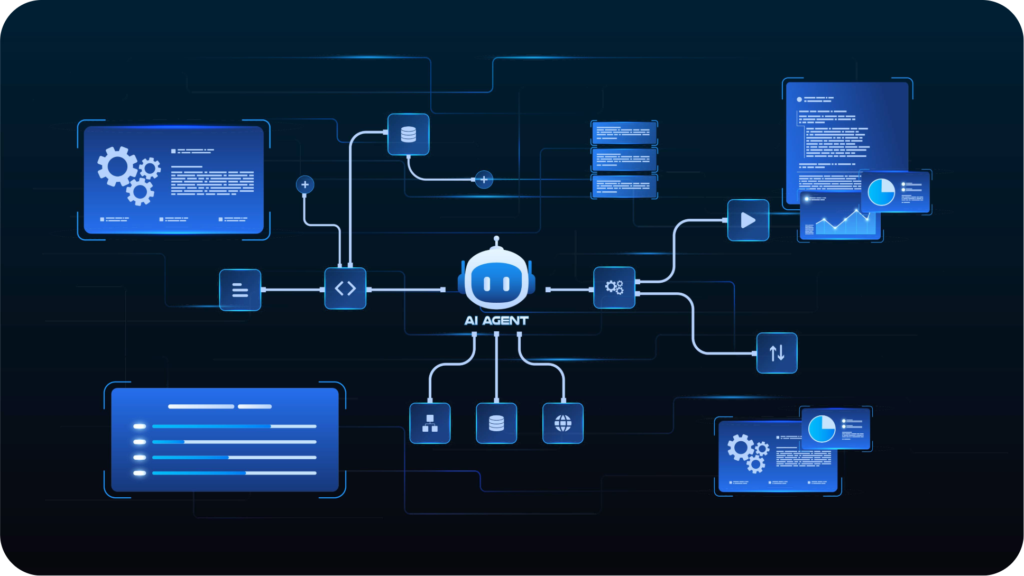
| Security Lifecycle Role | ThreatModeler | Frontier Models |
|---|---|---|
| Primary contribution | Operationalizes threat modeling across the SDLC | Accelerate vulnerability discovery and remediation |
| Starting point | Architecture diagrams, documentation, IaC, cloud context, system intent | Existing software, code, and systems to analyze and secure |
| Best used for | Understanding what could go wrong in design and where controls belong | Finding and helping fix issues in implementation |
| Core value | Secure-by-design decisions, governance, documentation, repeatability | Faster detection, exploit understanding, triage, and patching |
| System context | Architecture-aware, trust-boundary-aware, design-first | Stronger when paired with design and architecture context |
| Workflow role | Upstream design-time operating layer | Downstream vulnerability and remediation acceleration layer |
ThreatModeler captures how a system is designed—not just what code exists. That lets teams identify threats, attacker paths, trust boundaries, and control gaps earlier, when they are cheaper and easier to address.
When vulnerabilities are discovered later, teams can use ThreatModeler’s architectural context to understand which findings matter most, how to fix them in line with intended design, and where broader control improvements may be needed.
Threat modeling is how teams translate architecture into security decisions. ThreatModeler turns that discipline into a scalable operating practice across the SDLC with workflow integrations, automation, reporting, and governance.
Prompt-based AI is fast, but variable. ThreatModeler uses AI inside a deterministic threat modeling framework so outputs are structured, reusable, reviewable, and repeatable.
ThreatModeler maintains the security ledger: the persistent record of architecture, threats, controls, decisions, updates, ownership, and rationale over time.

10x
more threat models created in a large enterprise deployment
50%
reduction in effort
5x
faster model creation
2900+
components
100+
protocols
No. They are valuable. It appears to be a major advance in AI-assisted vulnerability discovery and defensive remediation. The point is that vulnerability discovery is not the same category as threat modeling.
Only partially. The stronger framing is that ThreatModeler solves the design-time security problem that frontier models do not solve.
Manual threat modeling can be. ThreatModeler is built to operationalize threat modeling with AI, automation, templates, integrations, and reusable content so teams can move faster without sacrificing consistency.
Because lower downstream remediation cost is still a downstream optimization. You are still paying to analyze, generate, validate, and implement fixes after design decisions have already propagated into code.
With AI-assisted remediation, those costs can expand further through repeated token usage, repeated tool execution, and repeated human review. And if the team never understood system intent in the first place, they may spend that effort addressing issues that are not the most important risks in context.
Yes. ThreatModeler’s MCP approach is designed to bring governed, deterministic threat intelligence into AI tools and AI-driven SDLC workflows.
