Faster at Every Step
What’s New in ThreatModeler 7.3
We’re excited to introduce our most powerful release yet! This update delivers significant performance enhancements across the platform, accelerating threat modeling workflows while strengthening security governance and compliance capabilities.
With intelligent automation features and streamlined processes, ThreatModeler 7.3 helps security and development teams work more effectively without sacrificing quality or governance.
Whether you’re focused on productivity, collaboration, or compliance, this release provides the performance boost needed to stay ahead of evolving threats.
Start Faster
Convert existing documentation and diagrams into threat models with intelligent import capabilities that automatically recognize and extract key elements, significantly reducing manual data entry when creating new models.
Image Importing: Convert Miro and XML diagrams and images into threat models with automated element recognition, enabling you to leverage existing documentation without starting from scratch.
Create Models from Existing Versions: Save valuable time by duplicating or branching proven models, maintaining consistency while adapting to new requirements.
Sprint Faster
Connect ThreatModeler with your existing development tools to create integrated security workflows without slowing development. These integrations enable teams to collaborate effectively without context switching, accelerating secure practices while maintaining velocity.
Bitbucket Linking (IaC-Assist): Streamline collaboration with integrated repositories, enabling direct connection between code and security models.
Enhanced Workflow Integration: Work more efficiently with improved connections to project management and development platforms including Jira, Azure, and various DevOps tools, enabling better tracking and management of security issues within your existing workflows.
Single Sign-On (SSO): Simplify authorization with group-based permission mapping, reducing administrative overhead while maintaining security.
Find Faster
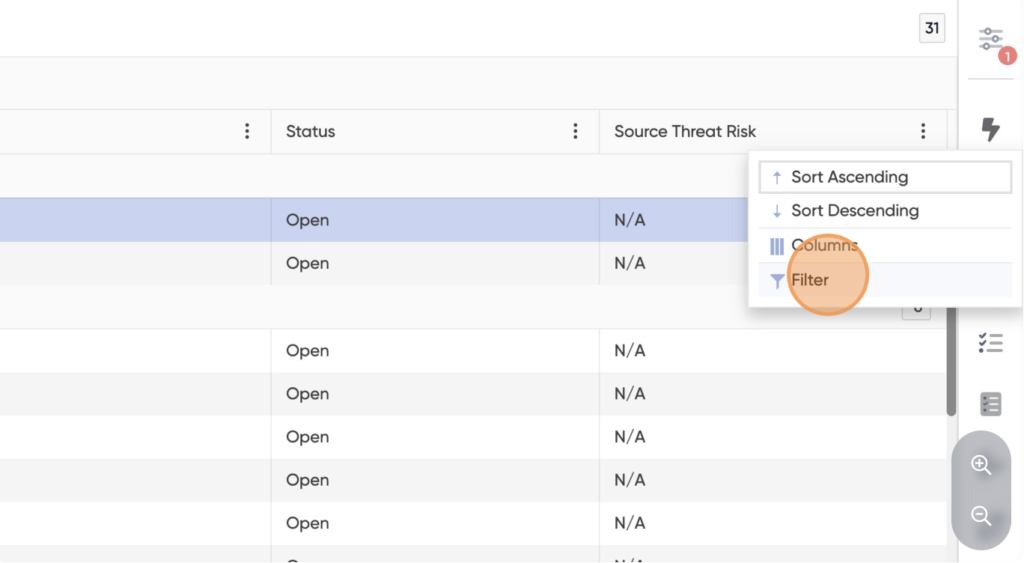
Locate and implement security controls with enhanced filtering capabilities that dramatically reduce time spent searching through requirements, enabling teams to focus on implementation.
Compliance-Focused Filtering: Streamline regulatory audits with targeted searches that map directly to compliance frameworks like NIST 800-53, making it easier to demonstrate adherence to specific standards.
Tag-based Filtering: Locate items faster with partial or exact match options, reducing time spent searching for relevant components.
Filter Threat Framework Entities: Export filtered threats, security requirements, and test cases into CSV format for further analysis or documentation.
Component Group Color-Coding: Improve readability in complex diagrams by visually distinguishing between different types of components.
Govern Faster
Establish consistent security practices across your organization with standardized workflows and improved governance tools that can be applied uniformly across teams, improving overall security posture while reducing compliance friction.
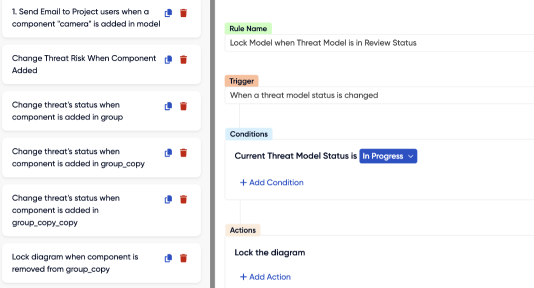
Diagram Locking: Maintain governance and integrity by locking diagrams based on specific conditions, preventing unauthorized changes to approved models.
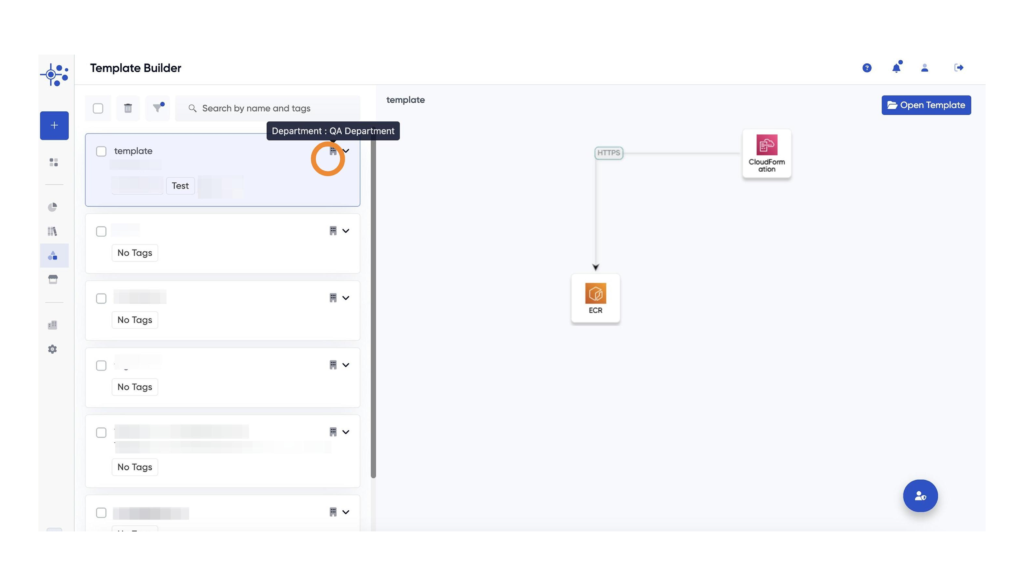
Modeling Templates: Promote standardization by sharing reusable modeling templates across teams, ensuring all models follow organizational best practices.
Show Hidden Entities as Disabled: Maintain visibility of all associations without affecting active components and reports, providing a complete view of your security landscape.
Mandatory Naming Warnings: Ensure proper labeling for consistent documentation, improving traceability and reporting accuracy.
Product Walkthroughs: Accelerate user onboarding with new, in-platform guided walkthroughs of key screens, including Threat Model, Diagram, Threats, Security Requirements, and Test Cases.