Choose Apiiro if you need:
• Continuous code-level visibility without architectural grounding
• Vulnerable code risk discovery without prevention
Apiiro can help.
ThreatModeler Platform &
Apiiro Design shifts vulnerability scanning left. ThreatModeler helps you define what secure looks like at scale, so you know what could go wrong before it’s built, and have the threat traceability matrix to show it.
AI can find vulnerabilities, but finding design flaws starts by defining what secure should look like: architecture, trust boundaries, data flows, and controls. ThreatModeler AI helps you do this at scale.
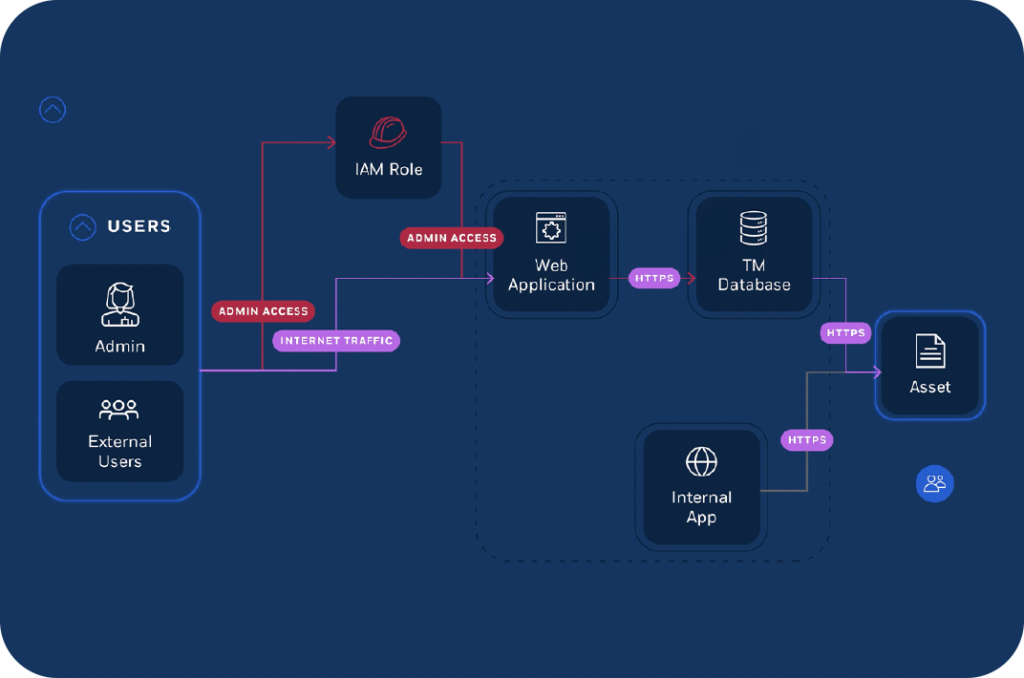
ThreatModeler turns requirements, diagrams, cloud context, IaC, and design artifacts into governed threat models product security teams can scale for repeatability and consistency.
ThreatModeler creates the system of record for threats, mitigations, ownership, rationale, approvals, and the threat traceability matrix, enabling transparent, purposeful, secure-by-design decisions.
| Capability | ThreatModeler | Apiiro |
|---|---|---|
| Primary approach | Architecture-driven threat modeling | Code & repository analysis |
| Security focus | Design-time risk identification & control design | Code-level risk discovery |
| Audit-readiness | Structured, compliance-mapped outputs | Not designed for audit evidence |
| Framework alignment | 180+ frameworks | No formal methodology or compliance alignment |
| Consistency of output | Deterministic, repeatable | AI-generated, variable |
| System of record | Persistent, governed threat models | Dynamic analysis, not authoritative |
| Scope | Full system architecture (apps, cloud, AI, APIs) | Application & code context |
| Reusability | Models, patterns, and controls reused across systems | Limited reuse across environments |
That’s where code-centric approaches break down.


This is what enables secure-by-design at scale.
• Continuous code-level visibility without architectural grounding
• Vulnerable code risk discovery without prevention
Apiiro can help.

✅ Consistent, enterprise-wide threat modeling to see and prevent risk
✅ Audit ready outputs with governed AI usage
✅ Architecture-driven security decisions that follow the SDLC
✅ A system of record for risk throughout the application lifecycle
ThreatModeler is built for this!
10x
more threat models created in a large enterprise deployment
50%
reduction in effort
5x
faster model creation
2900+
components
100+
protocols
