10x
more threat models created in a large enterprise deployment
ThreatModeler Platform &
AI speed plus architecture-aware secure design.
Project Glasswing accelerates vulnerability discovery and remediation. ThreatModeler ensures patches are grounded in system intent, trust boundaries, and architectural context.
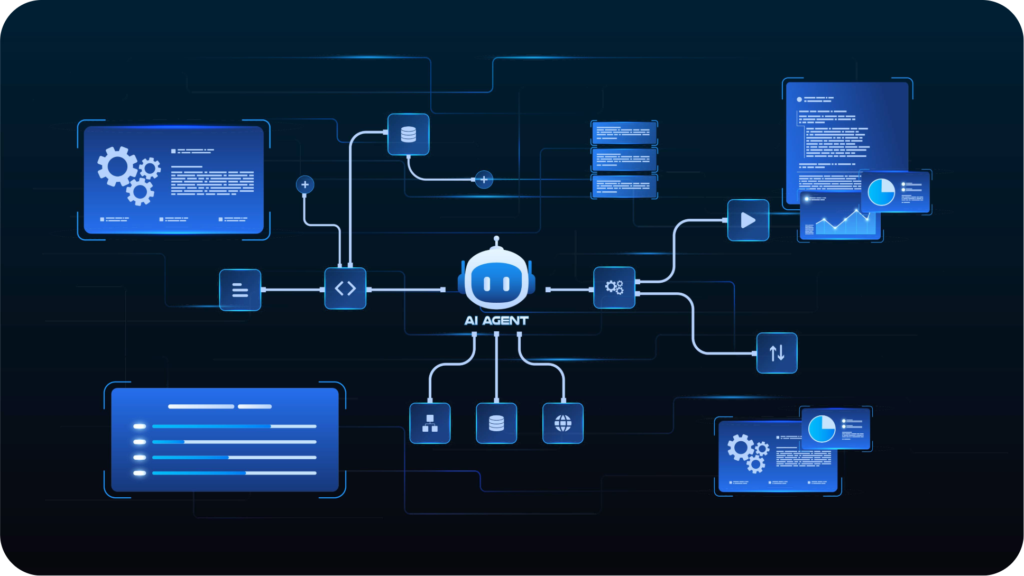
AI is helping businesses generate code faster. ThreatModeler captures architecture and intent, and recommends countermeasures, so teams and agents can fix security flaws faster. All powered by the industry's most robust threat framework.
ThreatModeler scales threat modeling across the enterprise with deterministic threat mapping, AI and process governance, and a system of record, enabling you to continuously identify and reduce risk across apps, cloud, and agents.
Faster remediation is most valuable when it is guided by that understanding.

Result: better AI output, stronger prioritization, less wasted remediation.
ThreatModeler operationalizes this with AI inside a deterministic framework, so security decisions are consistent, repeatable, and governed across the SDLC.
| ThreatModeler | Glasswing | |
|---|---|---|
| Primary contribution | Operationalizes threat modeling across the SDLC for an enterprise-wide view of risk and a control plane to manage it | Accelerates vulnerability discovery and exploitation |
| Starting point | Architecture diagrams, documentation, IaC, cloud context, system intent | Existing software, code, and systems to analyze and secure |
| Best used for | Understanding what could go wrong, documenting, and mitigating —starting with design and continuing across the SDLC | Finding and exploiting vulnerable code in production |
| Core value | Faster risk reduction with a secure-by-design system of record, design-flaw identification, governance and policy enforcement, and enterprise readiness | Expert vulnerability detection and exploitation |
| System context | Architecture-aware, trust-boundary-aware, secure-design system | Inferred and non-deterministic context |
| Workflow role | Architecture & Design, continuing across the entire SDLC | Downstream vulnerability and remediation acceleration layer |
When systems span cloud services, APIs, agents, data stores, identities, and infrastructure, teams need to understand how the system is supposed to work before they can decide which findings matter most.
A vulnerability may be technically real but not equally meaningful across every architecture. We’ve already seen this with a large number of Mythos findings. Threat modeling helps teams evaluate findings in the context of trust boundaries, attacker paths, exposure, compensating controls, and business impact.
When teams already know the intended design, the trust model, and the relevant control strategy, they can fix issues in ways that strengthen the system instead of just closing isolated findings.
AI can reduce the effort needed to generate fixes, but without architecture-aware context, it cannot choose which fix to implement, or if it should at all.
The goal is not just to remediate faster. It is to continuously reduce preventable risk by improving architecture, standardizing security decisions, and creating a repeatable system of record.

ThreatModeler captures how a system is designed, not just what code exists. That lets teams and agents identify threats, attacker paths, trust boundaries, and control gaps earlier, when they are cheaper and easier to address.
When vulnerabilities are discovered, teams and agents can use ThreatModeler’s architectural context to understand which findings matter most, how to fix them in line with intended design, and where broader control improvements may be needed.
Threat modeling is how teams and agents translate architecture into security decisions. ThreatModeler turns that discipline into a scalable operating practice across the SDLC with workflow integrations, automation, reporting, and governance.
Prompt-based AI is fast, but variable. ThreatModeler uses AI inside a deterministic threat modeling framework so outputs are structured, reusable, reviewable, and repeatable.
ThreatModeler maintains the security ledger: the persistent record of architecture, threats, controls, decisions, updates, ownership, and rationale over time. This becomes your most valuable asset.

10x
more threat models created in a large enterprise deployment
50%
reduction in effort
5x
faster model creation
2900+
components
100+
protocols
No. It is valuable. It appears to be a major advance in AI-assisted vulnerability discovery. The point is that vulnerability discovery is not the same category as threat modeling. Fixing bugs, is not the same as avoiding or remediating architectural flaws.
No, both ThreatModeler and Project Glasswing have their place. And in fact, both become stronger when combined. Still, it is important to understand where vulnerability detection and threat modeling differ.
Manual threat modeling is a slow process. ThreatModeler has solved that with an enterprise platform built to scale across the enterprise and keep pace of AI. The ThreatModeler platform operationalizes threat modeling with AI, automation, templates, integrations, and a curated threat library, so teams can move faster without sacrificing consistency. So you get a single enterprise-wide view of risk across apps, cloud, and agents and the control-plane to manage it.
The first myth is that Project Glasswing is reducing remediation costs. In-fact, software architects who have examined the Mythos findings have noted that many of the spotted defects were already mitigated by other security controls. Without proper security context, AI will find, fix, and likely create new vulnerabilities in an endless loop.
You can reduce some of the waste with repeated human review, but the human in the loop will need the same security and architectural context that the agent should have had in the first place. And that’s why vulnerability scanning and remediation alone, is not enough.
Yes. The ThreatModeler Platform built on an MCP agentic architecture. Our platform is designed to combine governed AI (BYOAI), with the industry’s most robust deterministic threat library. Available through our SaaS application, API endpoints, developer tools integrations, or MCP agentic workflows — ThreatModeler is designed to fit directly into your AI tools and AI-driven SDLC workflows.
